About Us
Helping businesses simplify their IT since 2014
We have solid experience in streamlining technology and ensuring that your business is compliant
Founded in 2014, Uzado is a Canadian-based company, with operations across Canada and the United States. We provide 24/7 Cybersecurity and Compliance Services that align our clients’ goals with their partners and government contractual mandates. We focus on using insights to drive business decisions. Our specialists don’t leave strategies to chance by analyzing data and showing what changes to make, and how to make them. Uzado offers multiple services to help companies simplify IT, centralize Cybersecurity management, and meet compliance standards. We can also customize our services so that we work with your existing IT network and programs.

Managing Your Journey with Uzado’s Life Cycle
By understanding the ins and outs of your technology, we can execute the best methodology to constantly improve and fully optimize your systems with data-driven insights. Here’s what happens throughout your journey with Uzado:
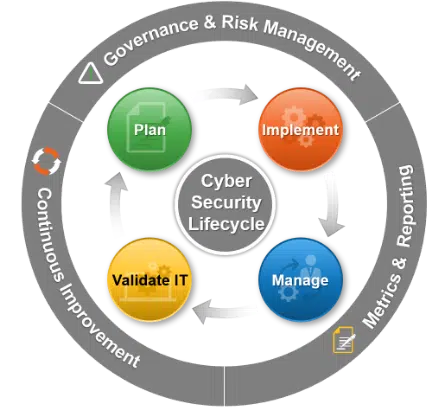
Uzado’s Life Cycle does not end at “validating IT.” Users can go through the cycle as many times as necessary to reach specific goals and optimization. This continuous aspect starts from planning and implementing improvements to managing and validating the changes to ensure effectiveness.
Uzado will provide your organization with actionable metrics where you will be able to see your progress from the start. Reports are available instantaneously or periodically – however you choose. The Dashboard feature on the platform allows users to view KPI metrics that are updated in real-time. The insights report provides more detailed information with the option of including our consultant’s comments.
It’s becoming more and more important for organizations to report cybersecurity activities and strategies to board members and C-suite executives. Uzado’s platform allows users to securely communicate with stakeholders and provide evidence of actions and events.
Driving business growth with a secure and compliant IT system
At Uzado, we recognize that businesses need to have a well-protected IT infrastructure that meets regulatory standards to stay ahead of the competition. With our expertise in cybersecurity and compliance, your company’s growth potential is limitless.
Recommend Uzado
Uzado takes pride in providing top-tier IT solutions and exceptional service to our clients, and we are committed to giving the same level of service to your contacts. Simply fill up the form for partnership opportunities and we’ll reach out as soon as possible!
